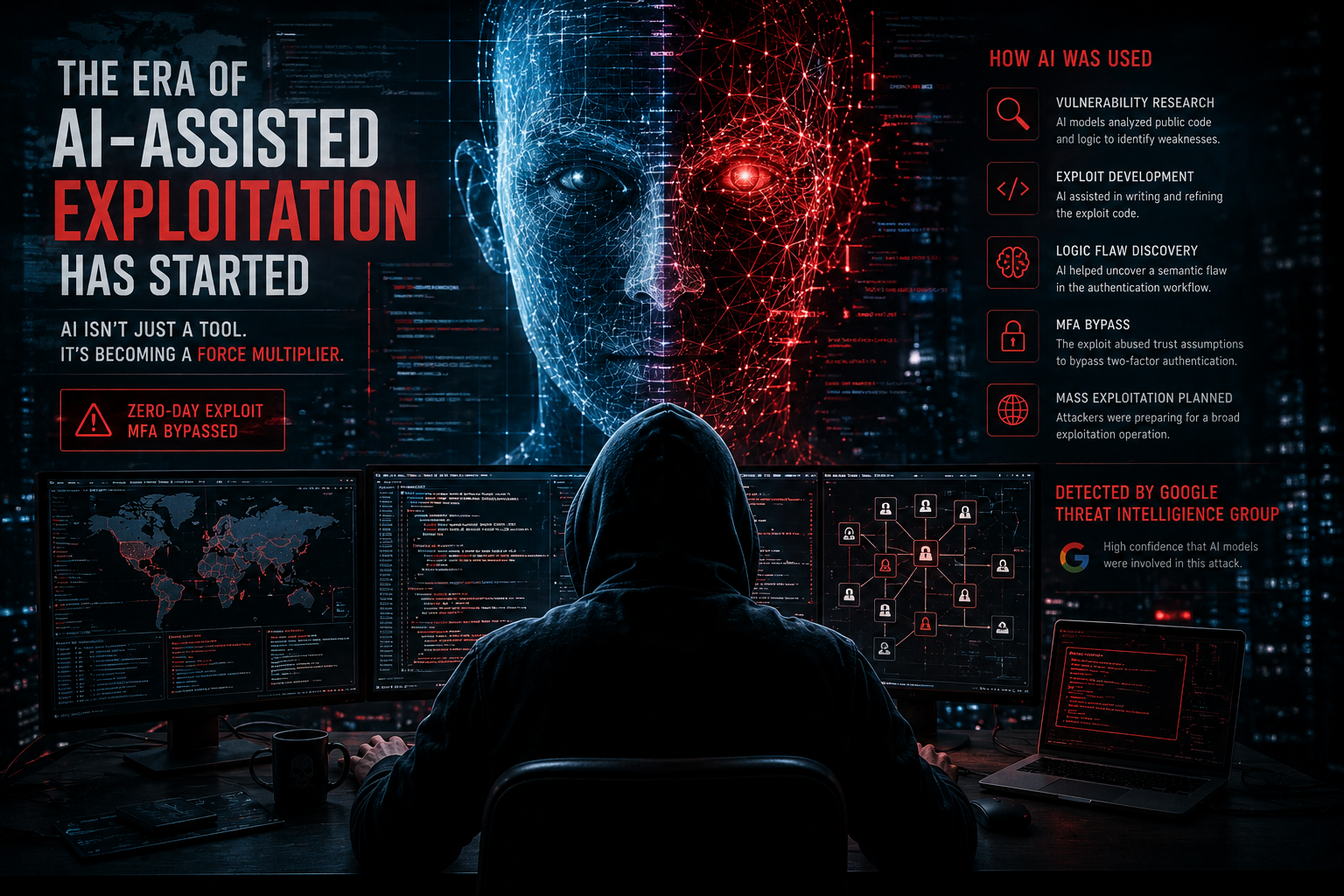
The Era of AI-Assisted Exploitation Has Started
A new Google report suggests attackers are already using AI during exploit development to accelerate real-world offensive operations.
Real-world insights on penetration testing, vulnerabilities, and how attackers identify weaknesses.
A new Google report suggests attackers are already using AI during exploit development to accelerate real-world offensive operations.
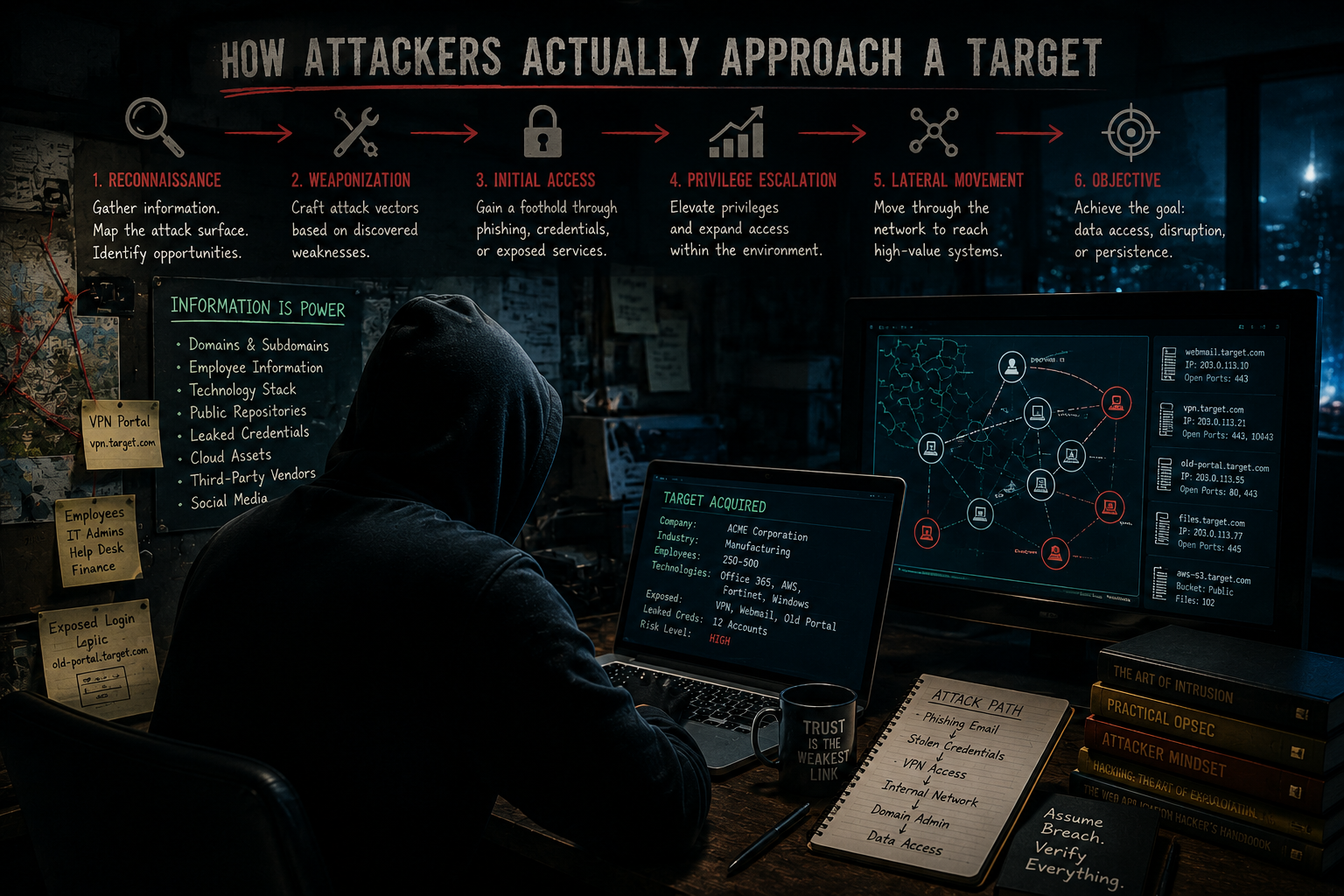
Understand how attackers use reconnaissance, exposed data, and chained weaknesses to map targets before they ever attempt a breach.
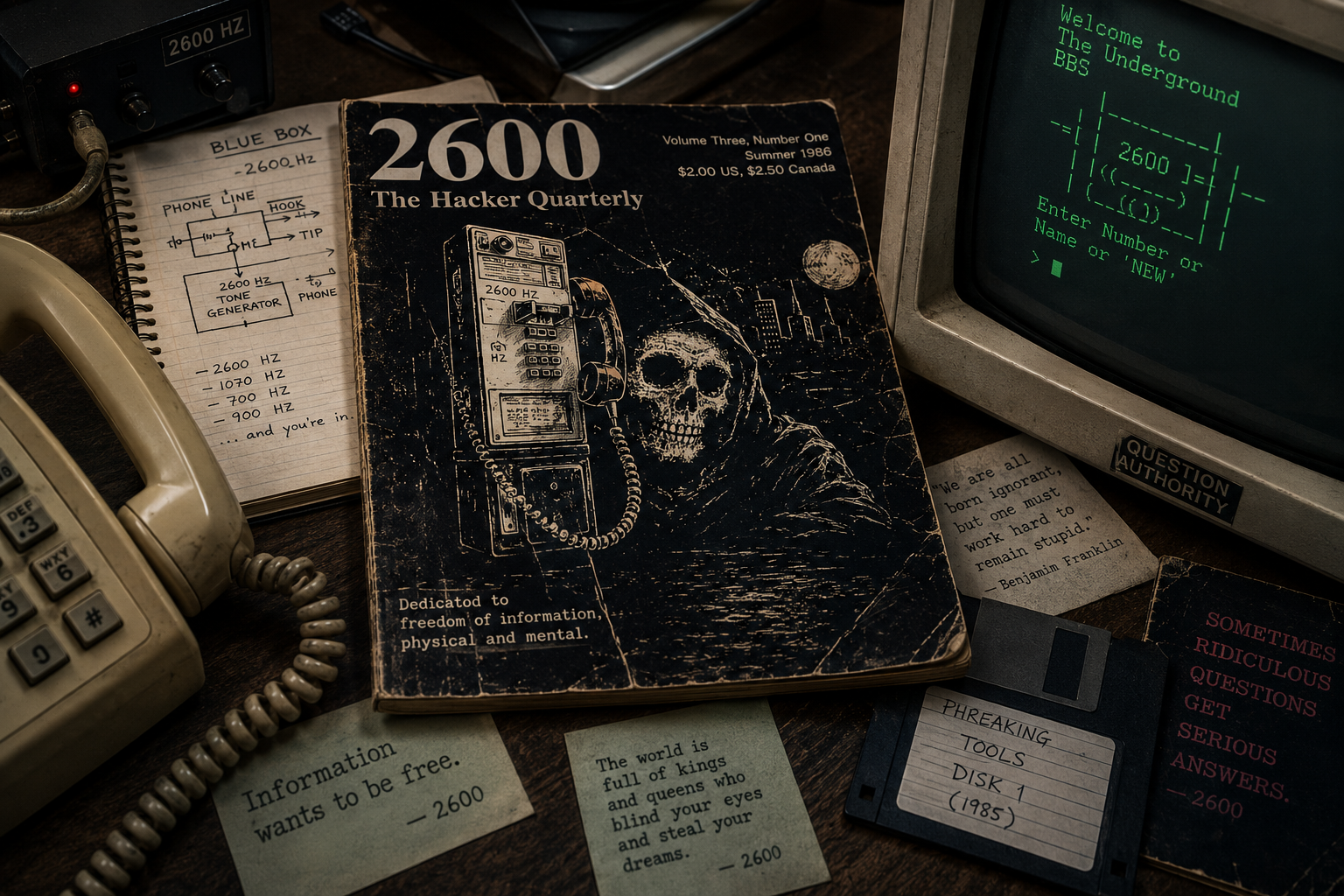
Explore the history of hacker knowledge sharing through 2600 Magazine and how it compares to modern learning methods.
A practical explanation of what penetration testing is and when your business actually needs it.

Understand the real difference so you can choose the right security approach.

Learn how attackers find exposed systems before they ever log in.