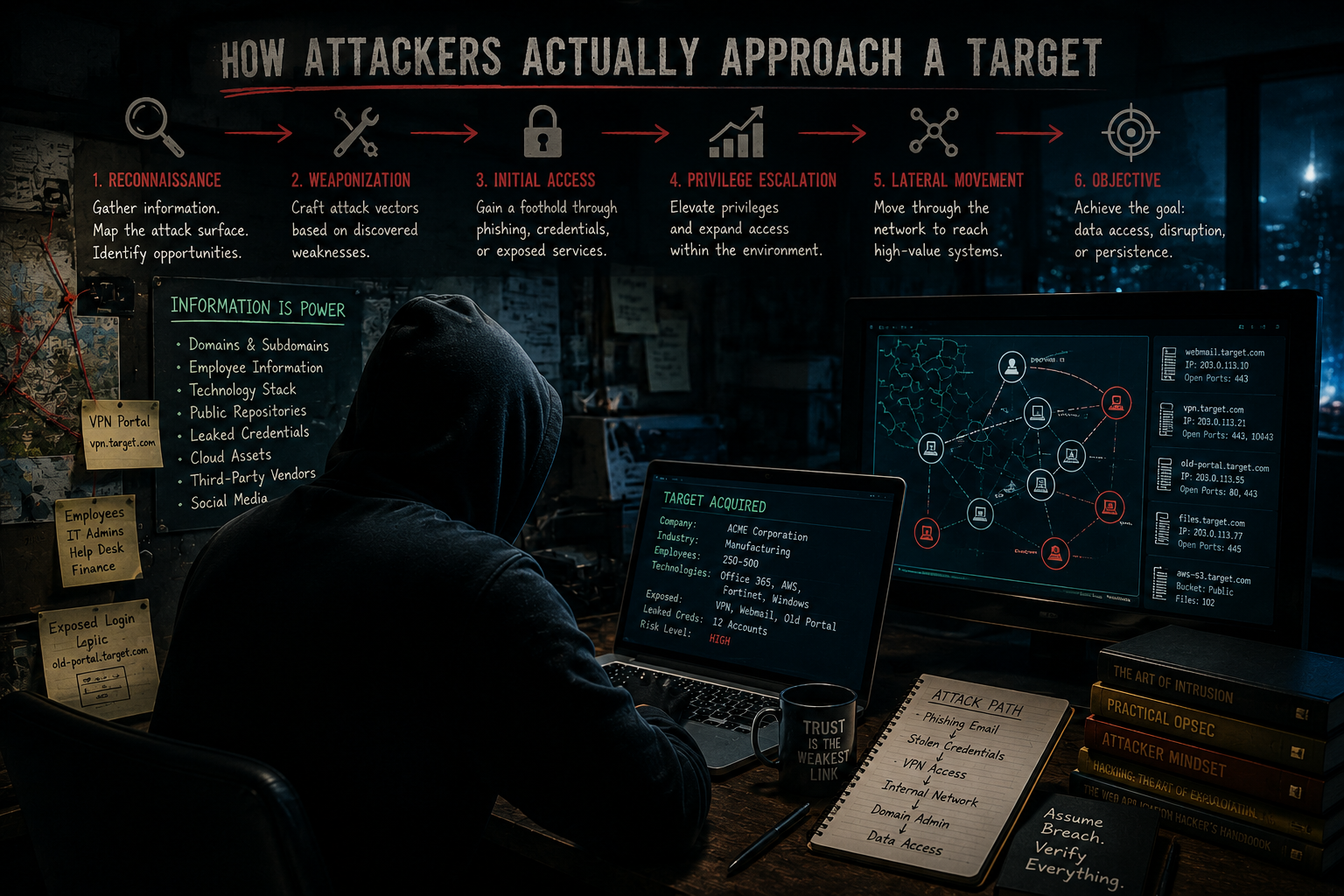
How Attackers Actually Approach a Target
Most attacks don’t begin with brute force. They begin with information.
Key Takeaway
Real attackers build paths from information and small weaknesses, not from single cinematic exploits.
Information is the starting point
When most people think about cyberattacks, they picture dramatic scenes from movies — someone in a dark room rapidly typing commands while sophisticated malware tears through a network in seconds. In reality, many attacks begin somewhere much quieter.
They begin with research.
Reconnaissance before exploitation
Before a password is guessed or a vulnerability is exploited, attackers are often spending time gathering information. Public websites, employee names, leaked credentials, forgotten infrastructure, exposed login portals, third-party vendors, and even social media posts can all provide useful pieces of a much larger puzzle.
Modern attacks are frequently built from information that organizations never realized they exposed in the first place.
People are part of the attack surface
The human element also plays a major role in modern attacks. Technology is important, but people are often easier to understand than systems. Attackers know this, which is why phishing, impersonation, MFA fatigue attacks, and help desk manipulation continue to be effective across organizations of every size.
Many attacks succeed not because security technology failed completely, but because trust was exploited somewhere along the way.
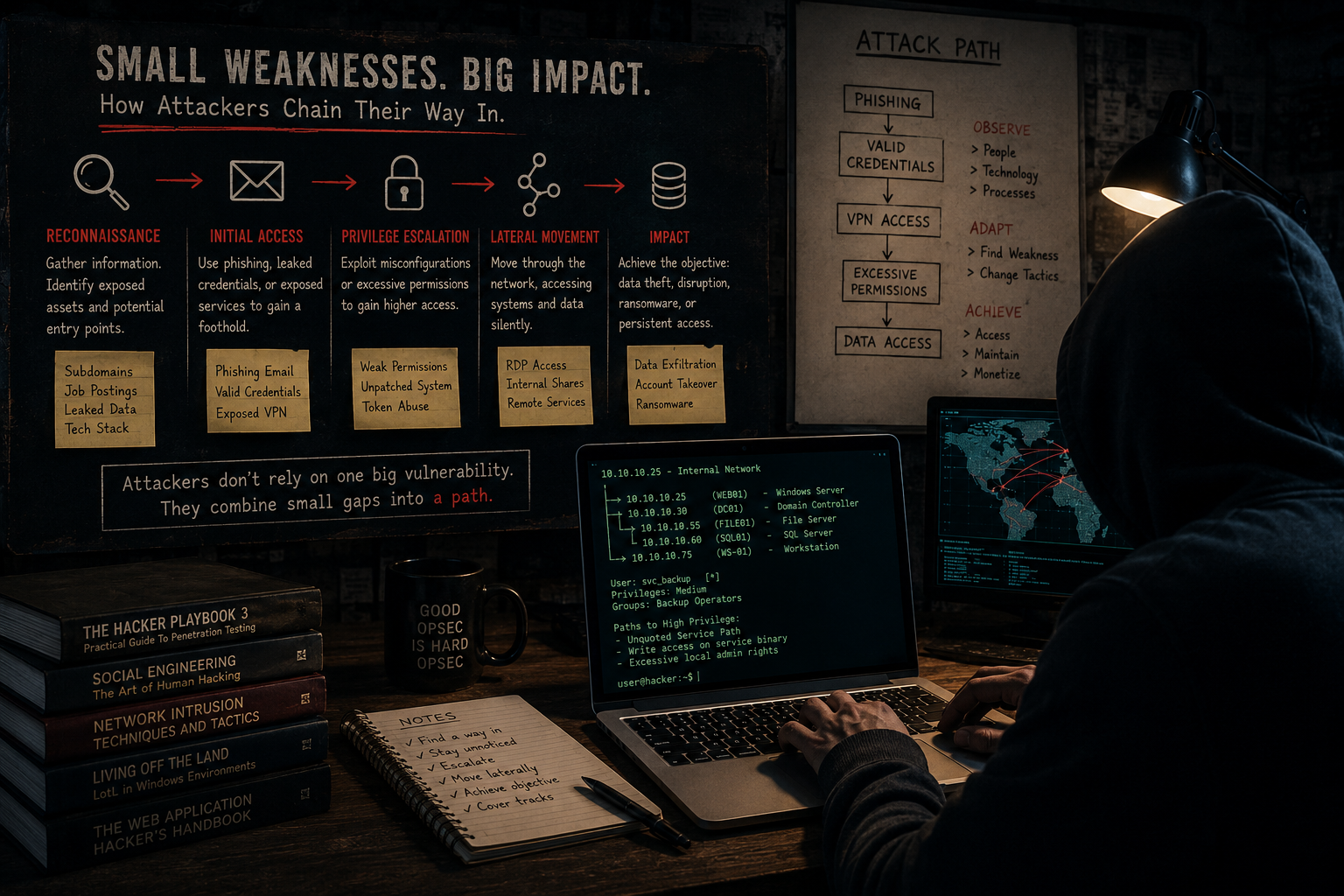
Small weaknesses form a path
Another common misunderstanding is the idea that attackers always rely on a single catastrophic vulnerability. In reality, compromises are often the result of several smaller weaknesses chained together. A reused password combined with missing MFA might lead to VPN access. Excessive permissions inside the environment might then allow lateral movement.
Individually, each issue may appear relatively minor. Together, they create a path.
Perspective is the strongest defense
This is why real-world penetration testing matters. Vulnerability scanners are valuable tools, but attackers do not think in isolated findings or severity scores. They think in opportunities, relationships, and attack paths.
Understanding how attackers approach a target is ultimately about understanding perspective. Security is not only about building stronger walls. It is about seeing the environment through the eyes of someone actively searching for weak points, blind spots, and opportunities that others missed.
Real-World Risk
Seeing your environment as attackers do reveals exposed details, human risk, and chained weaknesses before they can be abused.
Attack-focused security lessons
Related Articles
Need help validating real-world risk?
SecureProbe provides penetration testing, vulnerability assessment, and attack surface analysis services designed to identify practical security risks and provide clear remediation guidance.
Request an Assessment